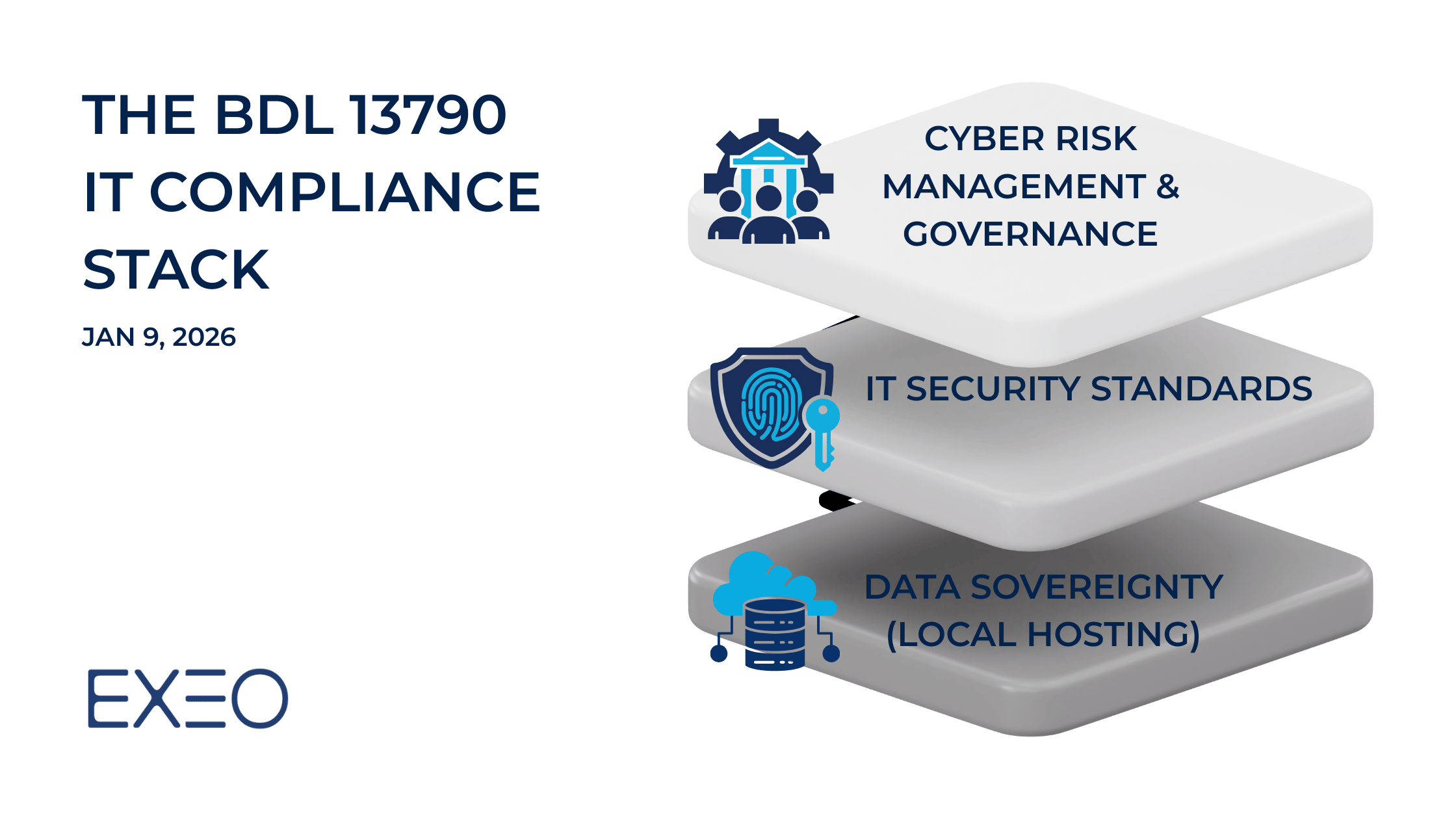
The BDL 13790 IT Compliance Stack: A Blueprint for Licensed Fintechs
Lebanon’s Fintech sector has a new rulebook. BDL Decision 13790 mandates strict local data hosting and advanced cyber governance for all payment providers. Discover how EXEO’s dual-site local cloud and vCISO services provide the compliant infrastructure foundation you need to secure your license.