Terraform Infrastructure as Code (IaC)
Infrastructure as code (IaC) explanation
Table of Contents
In contrast to physical hardware configuration or interactive configuration tools, infrastructure as code (IaC) refers to the process of managing and providing computer data centers through machine-readable definition files (code) using DevOps methodologies and versioning.
This procedure manages both physical and virtual computers, including bare-metal servers, as well as the configuration resources that go with them. Instead of maintaining the code through manual processes, the definition files or code uses scripts or declarative definitions to maintain the code.
With cloud computing, the number of infrastructure parts has increased, and new apps are being published regularly, requiring more dynamic infrastructure. This flexibility, and much more, is provided by Infrastructure as Code (IaC).
Infrastructure as Code benefits
Infrastructure as Code (IaC) gained several benefits as a result of its flexibility, including:
- Speed: This is the first important advantage of IaC; rather than spending the same amount of time setting up your infrastructure in each environment, Infrastructure as Code (IaC) allows you to easily build up your whole infrastructure by simply executing a script. This script will run in all environments, from development to production. Moreover in a disastrous event where all infrastructure fail, running the script will quickly generate the same infrastructure resulting in fast recovery and lower downtime.
- Cost Reduction: Time is currency. By automating the infrastructure process, engineers may spend more time executing higher-value tasks rather than completing manual work. Furthermore, the IaC script may automatically shut down environments when they are not in use, saving even more money on cloud computing costs.
- Consistency: Infrastructure as Code (IaC) reduces human error. In manual operations, humans and their memories are unreliable and prone to errors. Instead of having discrepancies caused by manual infrastructure management, Infrastructure as Code (IaC) overcomes this problem by having the same configuration file for each environment.
- Risk Reduction and Efficiency: Infrastructure as Code (IaC) also acts as a sort of documentation, so instead of worrying when your lead engineer -the only person who understands the ins and outs of your infrastructure setup- leaves, you now have a document that documents every step of the infrastructure. And, because configurations are bound to change, it might be difficult to pinpoint exactly what changes were made and who was in charge. Every change may be documented, reported, and monitored with Infrastructure as Code (IaC). As a result, if an issue arises with the new setup configuration, it can be identified and fixed much more simply, reducing risk and failure.
What is Terraform?
One of many tools for Infrastructure as Code (IaC) that is currently booming is Terraform by HashiCorp.
Terraform allows you to specify both Cloud and on-premises resources in human-readable configuration files (code) that you can reuse, distribute, and version.
Moreover, the lifecycle management and provisioning of all of your infrastructure can be done using a standardized methodology.
Terraform, in addition to handling high-level components like DNS records and SaaS services, can also handle low-level components like computation, storage, and networking resources.
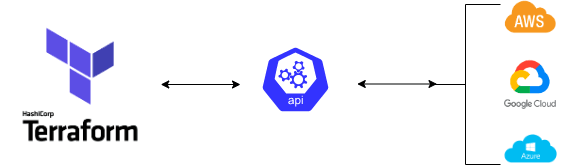
How does Terraform work?
Terraform uses application programming interfaces (APIs) to construct and manage resources on cloud platforms and other services. In other words, any platform or service like Azure, Google Cloud or AWS with an accessible API can be managed by Terraform.
What is the Terraform Workflow?
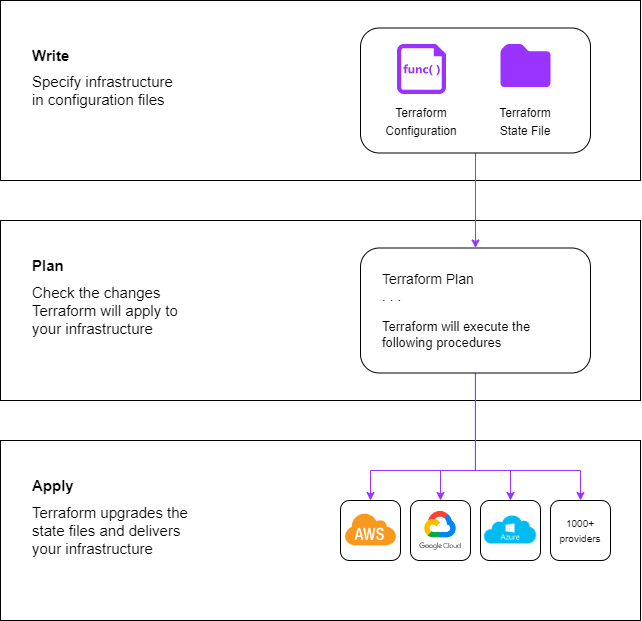
The core Terraform workflow consists of three steps:
- Write: You specify resources that may span several cloud providers and services. For example, you might construct a setup to deploy an application on virtual machines in a virtual private cloud VPC with security groups and a load balancer.
- Plan: Based on the current infrastructure and your setup, Terraform generates an execution plan that describes the infrastructure it will construct, update, or delete.
- Apply: After approval, Terraform executes the suggested operations with consideration for any resource dependencies. For instance, if you modify the characteristics of a VPC and alter the number of VMs in that VPC, Terraform will recreate the VPC before scaling the virtual machines,
What are Terraform UseCases?
Multi-Cloud Deployment:
When infrastructure is provisioned over multiple Clouds, fault tolerance is increased, this enables a more graceful recovery from Cloud provider disruptions. However, because each provider has its interfaces, tools, and workflows, multi-Cloud installations increase complexity. With Terraform, you can handle cross-cloud dependencies and manage various providers using the same procedure or script. For massive multi-cloud infrastructures, this makes management and orchestration simpler.
Application Infrastructure Deployment, Scaling, and Monitoring Tools:
Infrastructure for multi-tier applications may be efficiently deployed, released, scaled, and monitored using Terraform. N-tier application design offers a separation of concerns and allows you to scale individual application components. A pool of database-using web servers with additional tiers for API servers, caching servers, and routing meshes could make up an application. Together with handling tier dependencies automatically, Terraform enables you to manage the resources in each tier. When Terraform deploys a database layer, for instance, it does so before deploying the web servers that it depends on.
Self Service Cluster:
In a large company, your centralized operations team might deal with several recurring infrastructure requests. Terraform allows product teams to create “self-serve” infrastructure architectures that let them independently manage their infrastructure. Using Terraform modules that define the guidelines for delivering and managing services in your business, teams may deploy services fast and by your organization’s regulations. Ticketing systems like ServiceNow can be linked with Terraform Cloud to automatically generate new infrastructure requests.
Kubernetes:
Kubernetes, also known as K8s, is an open-source platform for managing, scaling, and automating the deployment of containerized applications. You may install Kubernetes clusters and manage its resources using Terraform (e.g., pods, deployments, services, etc.). Additionally, you may manage cloud and on-premises infrastructure with Terraform Cloud and a Kubernetes Custom Resource Definition (CRD) by using the Kubernetes Operator for Terraform.
Increase the benefits of Terraform and IaC in your organization
To maximize the benefits of Terraform and IaC in your organization, it’s useful to learn more and implement some proven practices. Some of these proven practices:
- Immutability is key: Immutable IaC notes that each component is built according to precise specifications, and there’s no room for individual deviations or fixes. After deployment, the servers or virtual machines are never upgraded or modified, which can reduce problems, increase security, and make it simpler to manage and document changes.
- Provide version control for IaC: Version control in IaC is especially important when it comes to configuration files. Why not version control them like you would version control any other code? IaC files need to be updated along with the IT environment they help manage. With improved traceability and visibility, you can simply track, manage, and restore any potential modifications to your systems using this technique.
- Ensure modularity in IaC: Small modifications and microservices are always simpler to handle than large amounts of work and complex monolithic code. Finding small, testable modifications in modules that can be implemented one at a time is always helpful. This complements the microservice architecture, which enables the creation, administration, and maintenance of programs as a number of deployable pieces.
- Be cautious of hard-coded secrets: Your organization may be in significant danger if your IaC code has exposed credentials. Having hard-coded secrets might expose passwords to attackers and result in failure of the authentication procedures. Avoiding storing such secrets in files submitted to web-based services like version control systems without utilizing secure secrets storage is a smart practice. In general, it’s preferable to restrict hard-coded secrets from entering the main branch in the first place. But if it goes unnoticed, it’s critical to search for exposed credentials in IaC. Code secrets may be found using a variety of methods, such as regular expression scanning (which looks for patterns in other secrets), keyword scanning (which looks for phrases like “password” that are connected with secrets), and entropy-based scanning (words that differ from a real language). In an initial evaluation, it’s just as vital to check for IaC security misconfigurations as it is to check for hard-coded secrets in the main branch and version history, one of the best tools to scan your script is Nessus Terraform Scanner.
In a nutshell
Whether they are working on cloud or on-prem -due to its numerous benefits- it is essential for any cloud provider and any DevOps engineer to be familiar with Infrastructure as Code in general and Terraform in particular in order to provision and manage environments.
As a Cloud Engineer there are three things you should keep in mind when it comes to Terraform:
- Every DevOps cloud deployment should be provisioned using IaC;
- Carefully design you Terraform workflow from writing to planning to applying;
- Always keep security in mind when implementing IaC.